The Case for Verifiable Open Source
How can websites earn the trust of their users?
What if google.com was open source? If the code revealed that user data was anonymized, storing only the minimum data required for advertising purposes (e.g. categorizations), we would all sleep better at night. There would be a massive drop in customer privacy inquiries. People might switch from other services; it would create a competitive advantage in the space.
If the open source code could be proven legally, it could simplify Google’s regulatory processes for GDPR and other emerging privacy acts such as the CCPA in California. If sensitive PII was not being collected, it could also alleviate some fear of a "PII armegeddon" currently priced into GOOG shares, and it could reduce the incentive for hackers to attempt to breach data stores.
| Legal | could simplify regulatory processes for privacy laws; current and future |
| Financial | analysts might price a stock favorably if the company did not store PII, as it could lead to expensive breaches under CPPA and other laws |
| PR | can validate any functional claim about the app via verifiable code |
| Information security | could reduce perceived incentive for hackers |
What is stopping Google from open sourcing their code today? The biggest reason is that there is currently no way for websites to confirm their code is actually running as claimed, so most of the aforementioned benefits would not be obtained. There would be constant allegations that the code running on their servers was different from the code revealed in their public repository. The legal, financial, and information security benefits would be reduced for the same reason.
There has never been a way for a company to prove claims about their website's functionality or PII collection; until now.
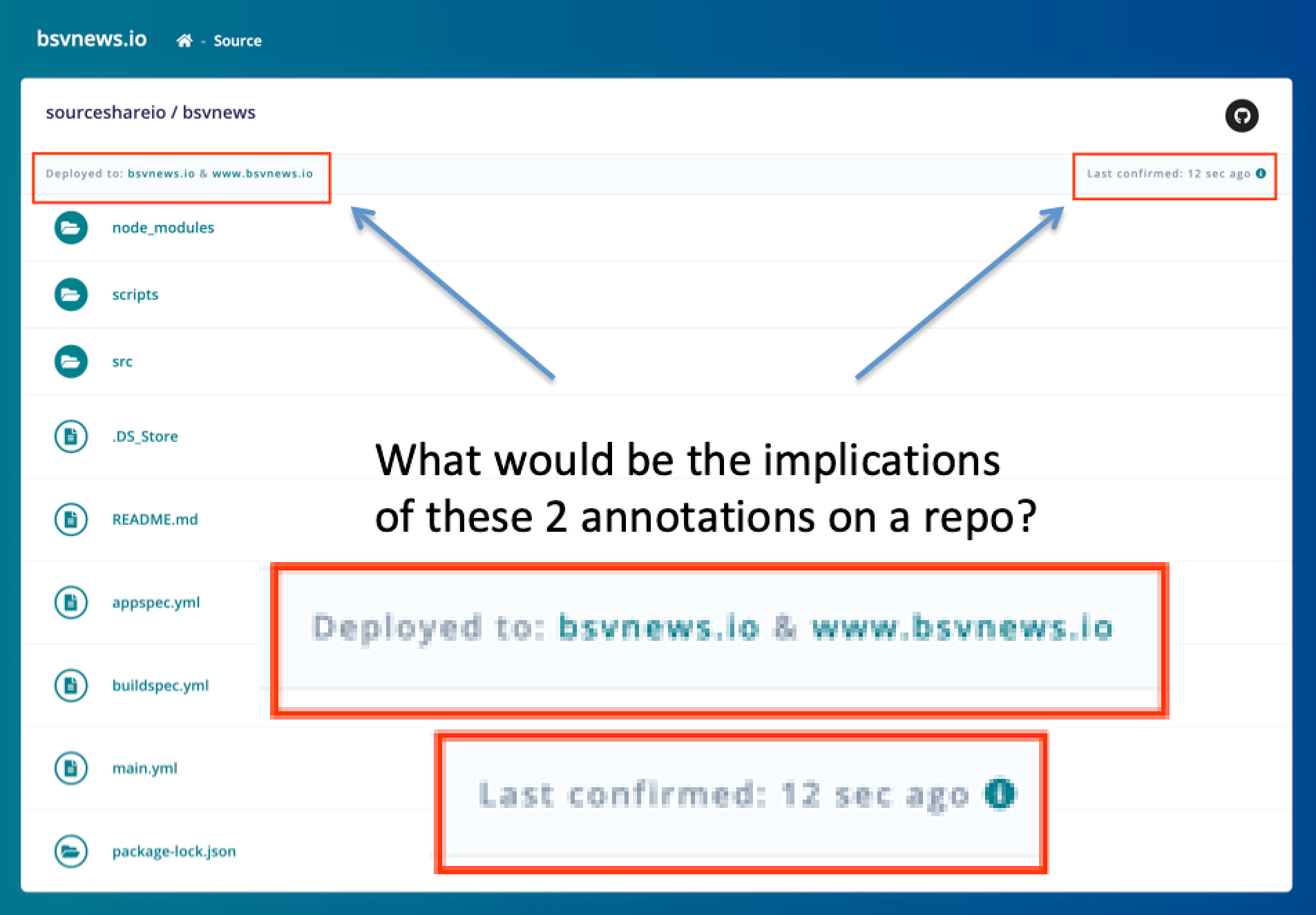
Thanks to advances in software and server architecture, it is now possible to prove what source code a website is using. The system which converts the code into a running application on the website is called a pipeline. Given a specific set of permissions, it is possible for a 3rd party to check the settings of each stage of the pipeline, to ultimately verify which code repository is being accessed from the website’s URL. It is then possible for the general population to check the code of the pipeline-checking script, so end users can be certain that the response has not been tampered with.
The result of this is that it can be proven which public code repository is being used by the servers of a given website, and the code can be reviewed to answer any privacy question a user may have.
Bringing verifiable open source to web applications could be a massive win for specific use cases. If you’re asking the user to go out on a limb and trust you on a claim, you are losing customers; but if you can prove it verifiably, you may win them back. If you would like to learn more about this system, please visit sourcereports.com or contact me via email.
